Analysis of DrugHub URL
Comprehensive operational history and feature review. Evaluating the cryptographic architecture, routing protocols, and milestone developments of this hidden service.
Executive Summary
DrugHub URL represents a sophisticated darknet platform operating exclusively as a Tor hidden service. Emulating the utilitarian design choices of its predecessors, the platform aims to provide a reliable, structured environment for the exchange of digital commodities and physical niche goods.
Observers note that the network relies heavily on minimizing attack surfaces through forced cryptographic authentication and limited JavaScript dependency. Established to circumvent the structural vulnerabilities of earlier hidden services, it has rapidly grown to support thousands of concurrent connections utilizing an advanced anti-DDoS proxy network.
Historical Timeline
Inception & Network Testing
Phase I
The platform's initial cryptographic signatures were observed on public key servers, indicating early localized testing of the hidden service architecture and database schemas.
Implementation of Strict Crypto Standards
Phase II
Infrastructure pivoted to an exclusively Monero (XMR) validation model. Bitcoin (BTC) support was permanently deprecated to prevent blockchain heuristics and metadata tracing by third-party analysis firms.
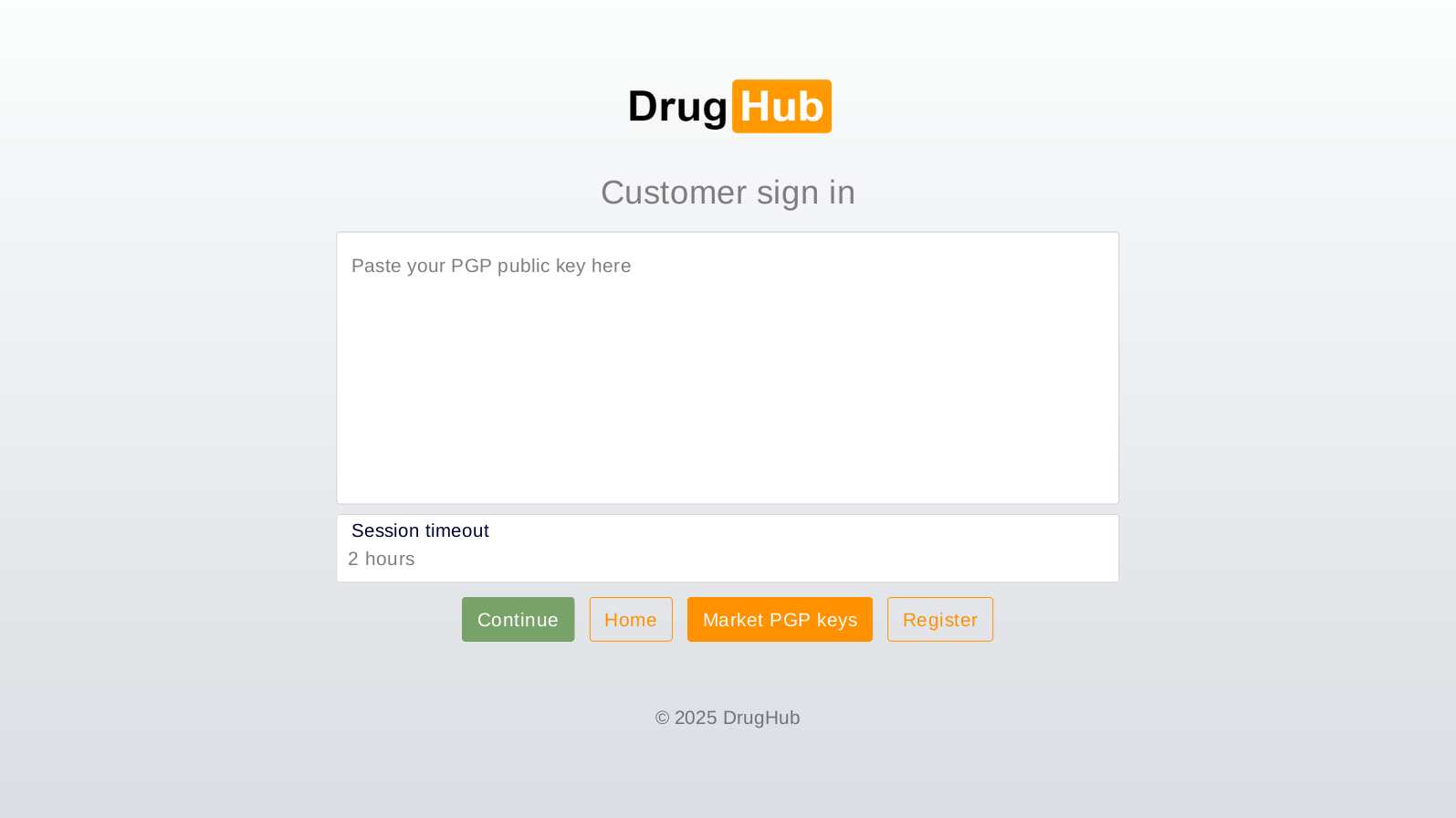
Passwordless Authentication Rollout
Phase III
The administration mandated PGP-only authentication. Traditional password inputs were eliminated, forcing users to decrypt challenges locally, effectively neutralizing credential stuffing and remote phishing operations.
Technical Architecture
-
XMR Exclusive Environment
Integration of Monero (XMR) ensuring default privacy. Transactions process via stealth addresses and ring signatures, obfuscating the sender, receiver, and volume of the transaction.
-
Walletless Modality
Funds are not stored on central platform hot wallets. Transactions utilize a direct-pay architecture where users transmit exact sums to generated single-use nodes, mitigating systemic loss during server seizures.
-
Multisig Escrow Protocol
Advanced 2-of-3 multisignature escrow protects participants. Funds require authorization from two separate cryptographic keys to release, preventing unilateral exit operations.
Security Posture
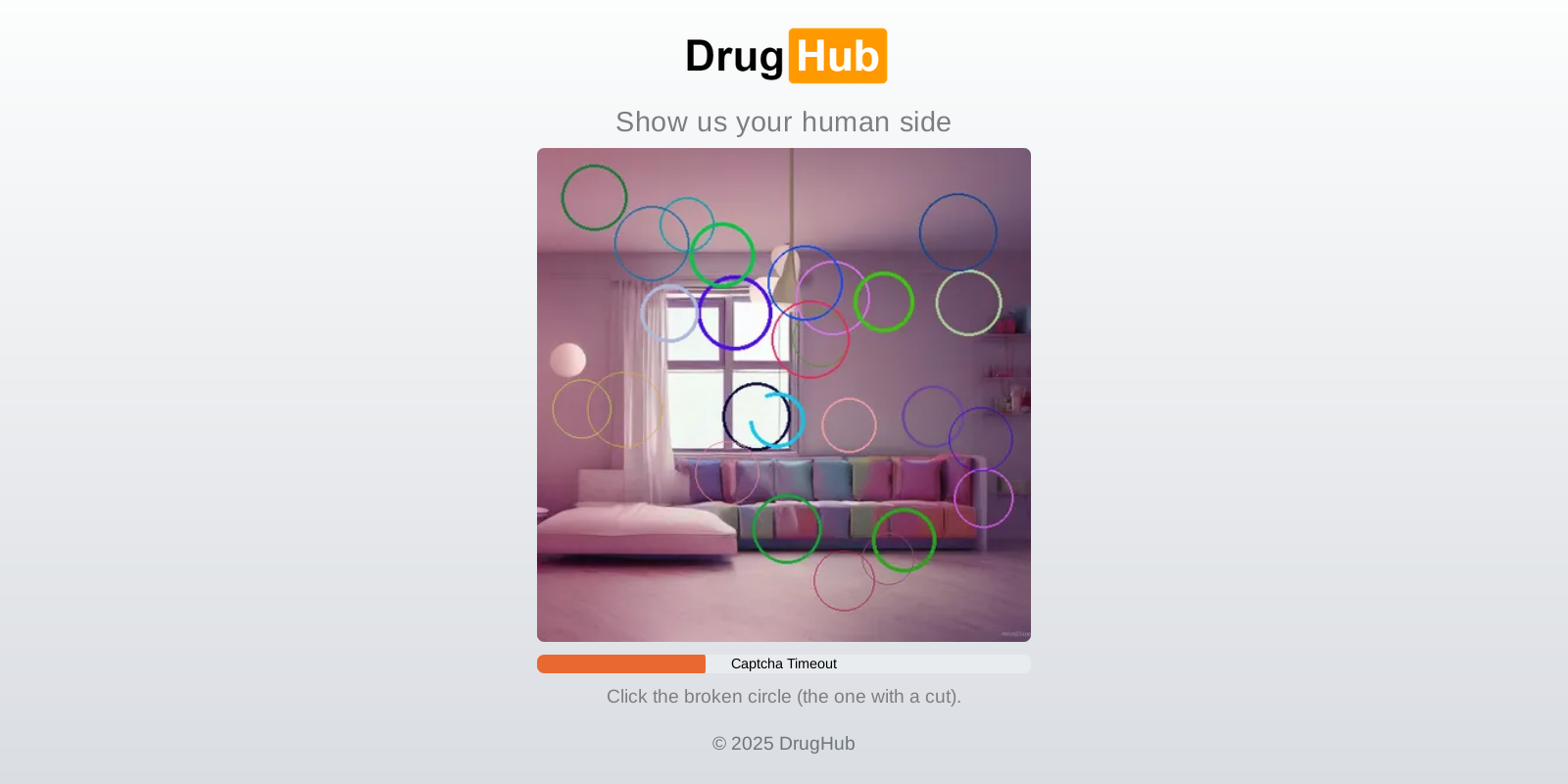
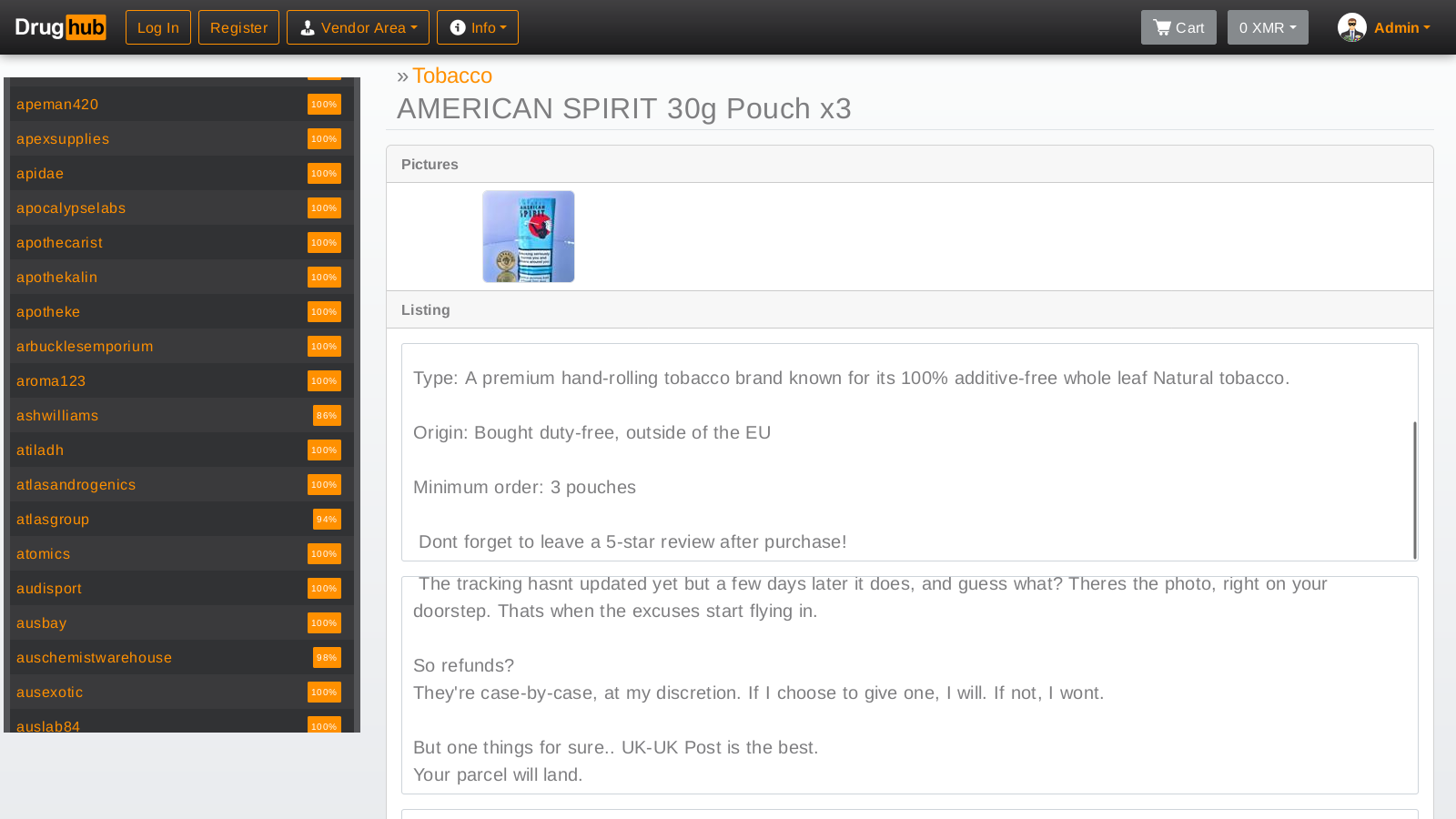
Platform Interface Preview
A visual examination of the internal routing architecture and user interaction screens. These captures demonstrate the front-end minimalist design required for low-bandwidth Tor environments.
Community & Operational Metrics
Merchant Verification Protocols
To maintain ecosystem integrity, prospective distributors must supply verifiable cryptographic credentials and fulfill strict financial bond requirements. These bonds act as an operational deterrent against short-term malicious behavior, solidifying the market's long-term reliance on reputable merchants.
Scaling Infrastructure
Research indicates the network supports tens of thousands of active cryptographic identities. The utilization of rotating Tor circuit relays combined with backend caching allows the platform to maintain high uptime percentages, even during sustained volumetric attacks on the core onion domain.